What Is Kerberos Protocol?

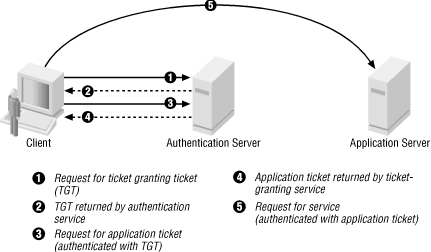
Kerberos is a computer-network authentication protocol that works on the basis of tickets to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner.
Kerberos builds on symmetric key cryptography and requires a trusted third party and optionally may use public-key cryptography during certain phases of authentication. Kerberos uses UDP port 88 by default.
Kerberos version 4 is an authentication system that uses DES encryption to authenticate a user when logging into the system. The authentication is based on ability of the sending system to use the common key to encrypt the current time, which the receiving system can decrypt and check against its current time.
Kerberos works by authenticating the user’s login password. A user enters kinit command, which acquires a ticket that is valid for the time of the session (or eight hours, the default session time) from the Kerberos authentication server. When the user logs out, the ticket can be destroyed (using the kdestroy command)
Kerberos version 5 protocol is implemented in both 2000 and windows XP and is used to provide a single authentication service in a distributed network. Kerberos interoperability provides a common protocol that allows a single user account database for authenticating users on all enterprise computing platforms to access all services in a heterogeneous environment.
Differences Between Kerberos Version 4 and Version 5 In Tabular Form
| BASIS OF COMPARISON | KERBEROS VERSION 4 | KERBEROS VERSION 5 |
| Year of Release | Kerberos Version 4 was released in 1980’s way before version 5 was released. | The Kerberos version 5 was published in 1993, 13 year after the release of Kerberos Version 4. |
| Principal Name | Kerberos version 4 Uses the principle name partially. | Kerberos Version 5 uses the entire principal name. |
| Encryption Techniques | Kerberos version 4 uses DES encryption techniques. | In Kerberos version 5, the cipher text is tagged with an encryption type identifier and therefore any type of encryption can be used. |
| Encoding | Kerberos version 4 uses the “receiver-makes-right” encoding system. | The Kerberos version 5 uses the ASN.1 coding system. |
| Ticket Lifetime | In Kerberos version 4, the ticket lifetime has to be specified in units of 5 minutes. | In Kerberos version 5, ticket one lifetime can specify an explicit start and finish times allowing arbitrary lifetimes. |
| Ticket Support | Ticket support is satisfactory in this version. | Ticket support is well extended. Facilitates forwarding, renewing and postdating tickets. |
| IP Addresses | Kerberos version 4 contains only a few IP addresses and other addresses for types of network protocol. | Kerberos version 5 contains multiple IP addresses for types of network protocols. |
| Key | Given that the same key is used repeatedly to gain a service from particular server, there is a risk that an attacker can replay messages from an old session to the client or sever. | In Kerberos version 5, this is avoided by requiring a sub session key which is used only for one connection. |