10 Difference Between Unit Testing And System Testing
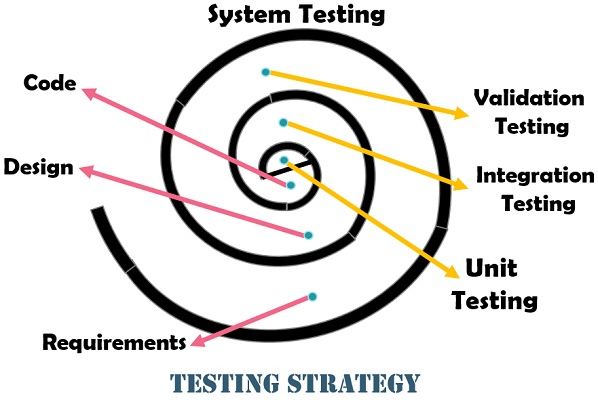
What Is Unit Testing? Unit testing is a software development process in which the smallest testable parts of an application known as units are individually and independently scrutinized for proper operation. This process can be done manually but it is usually automated. Unit testing involves only those characteristics that are vital to the performance of … Read more